Introducing the Stellar Cyber API 

Stellar Cyber provides a public API that lets you interact with the product programmatically, allowing you to write your own scripts to retrieve data from the product or create entities within it.
-
Stellar Cyber is always adding new public APIs to the product. The Summary of Public APIs, below, shows you the types of information you can retrieve and create.
-
Once you are ready to get started working with the API, use the following steps:
-
Use the information in Configuring API Authentication to create a user with the necessary privileges and an API key.
-
Use the detailed reference material from the API's swagger.json file to create your own scripts and API calls.
-
-
Refer to the Stellar Cyber Public API Examples for a set of sample scripts and API calls that you can use as inspiration for your own work.
Access to the API is only available using local user accounts. Single-sign on (SSO) users cannot access the API with their SSO credentials.
The API replaces access to port 8889 on the DP.
Relative Path to Stellar Cyber API Endpoints
The relative path to Stellar Cyber's public API endpoints is as follows:
-
https://<Platform Hostname>/connect/api/v1/<specific endpoint>
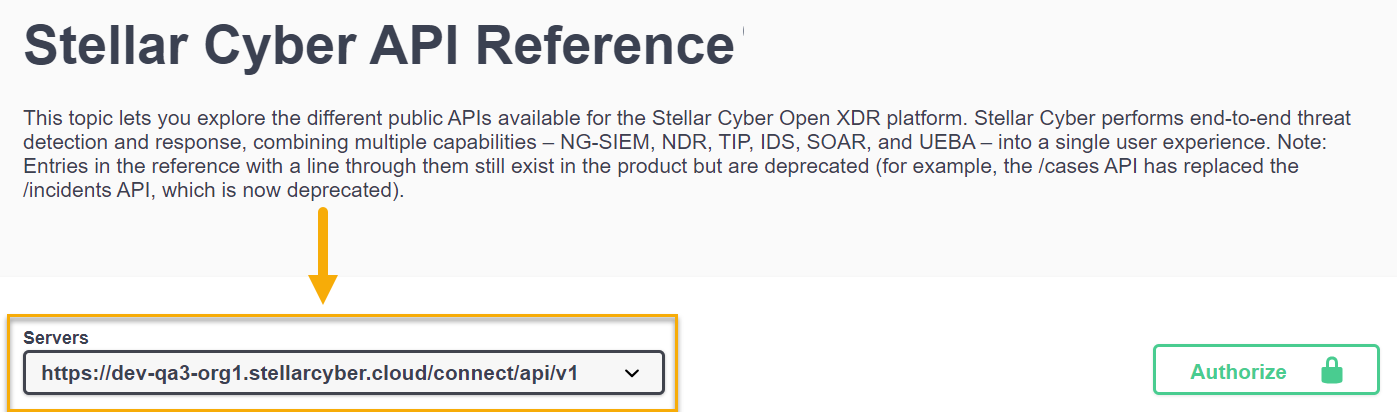
You can see this at the top of the Stellar Cyber API Reference in the Servers field. For example:
The individual endpoints shown in the API Reference do not include the relative path, but you must include it when accessing the public API outside of the swagger.json page.
Summary of Public APIs
As summarized in the interactive API Reference, Stellar Cyber provides public APIs for the following features:
-
Create, Delete, Edit, and List Connectors. You can also edit the checkpoint of a connector – the time from which it pulls data, which is useful in case of data loss.
When numerous connectors roll back checkpoints during regular operating hours, it can lead to increased resource consumption and potential process interruption due to circuit breakers. Consult with Customer Support for considerations regarding off-peak execution of checkpoint rollback.
-
Download Sensor Images

-
Retrieve Detailed Sensor Information
-
Retrieve Detailed Case Information
-
Retrieve Case Observables
-
Update Case Information
-
Retrieve information on Storage Usage
-
Retrieve Ingestion Statistics
-
Retrieve information on the configuration and hits of log filters.
-
Retrieve user activity logs for Stellar Cyber user accounts.
-
Create, Delete, Update, and List Tenants
-
Create, Delete, Update, and List Tenant Groups
-
Update Tags, Status, and Comments for Events
-
Perform an ElasticSearch Query on a Specific Index
-
Reset User Passwords
-
Add events to the Security Index (Bulk or Standard)
-
Create, Delete, and List Lookup Tables (by Tenant or by All Tenants)
-
Create, Delete, and List Reports
-
Create, Delete, and List Security Event Filters
-
Create, Modify, and Delete Data Analyzer Profiles